Leading fraud abatement since 2015
Long before mobile advertising fraud was on the radar for brand advertisers, sophisticated performance advertisers were learning that it was a costly and challenging problem. As a measurement provider for some of the highest-volume performance advertisers, Kochava recognized abnormalities in campaign data that in some cases were fraudulent. Thus, began the fight against mobile advertising fraud, and since 2015, we’ve been developing the most astute tools to prevent, identify, and abate it.
Networks caught in the middle of mobile advertising fraud
Mobile advertising fraud affects both marketers and networks alike. While the media like to focus on the challenges advertisers face in dealing with mobile fraud, the reality is that networks often get squeezed the hardest. Because networks typically have to pay publishers for traffic before advertisers are billed, networks end up holding the bag on losses from fraud.
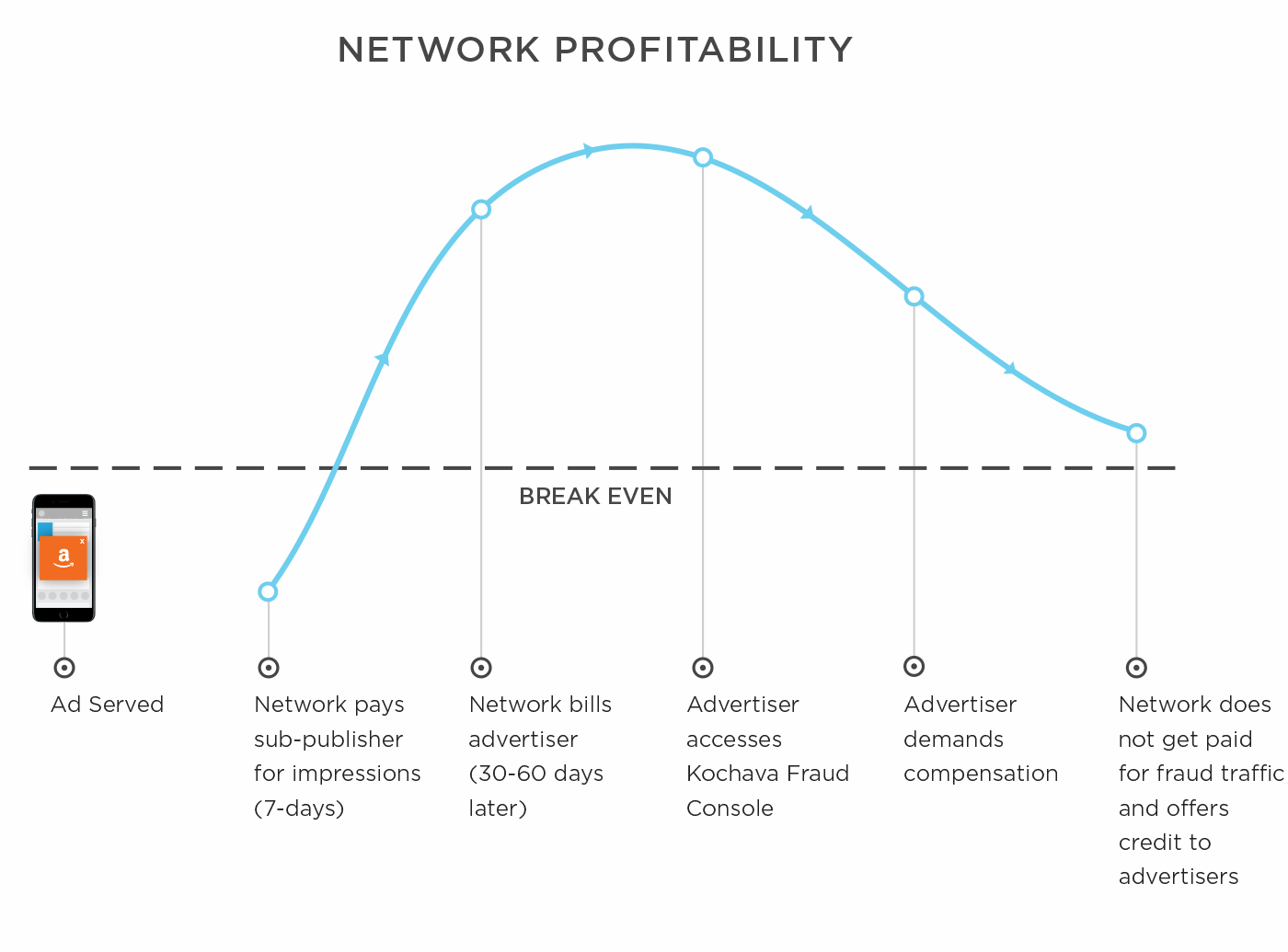
By the time advertisers reconcile the cost of their traffic against any fraud they detected during the campaign, networks have already paid for said traffic. Thus, networks are not only blindsided by reports of fraud but also stuck offering credit to advertisers for the fraudulent traffic they already paid for.
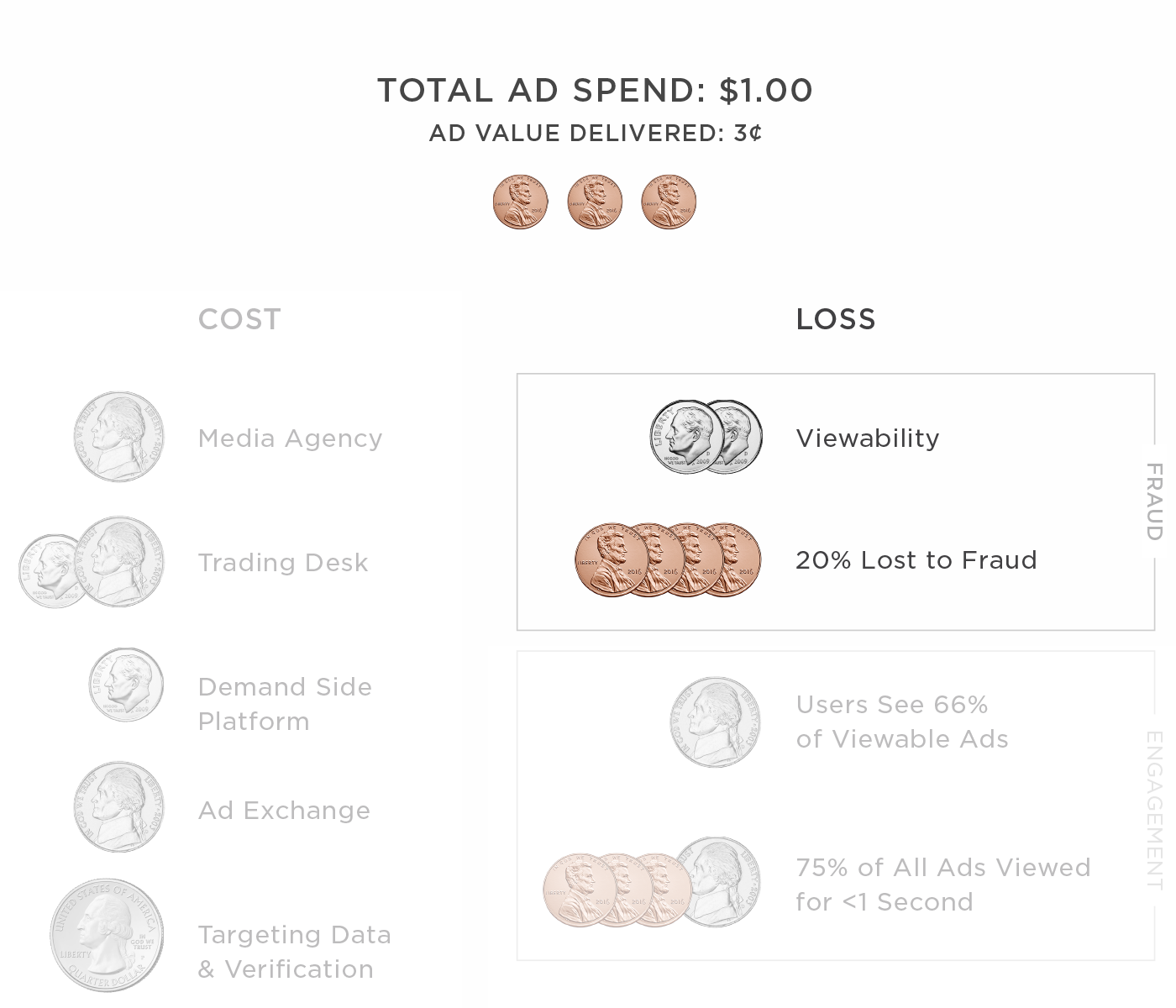
Fraud also eats into network profits. Out of the total ad spend, fraud diminishes the ad value for a campaign as well as a network’s credibility to advertisers. The competition for networks is already tough, as they compete with media agencies, trading desks, DSPs, ad exchanges and other service providers for market share.
Break a vicious cycle
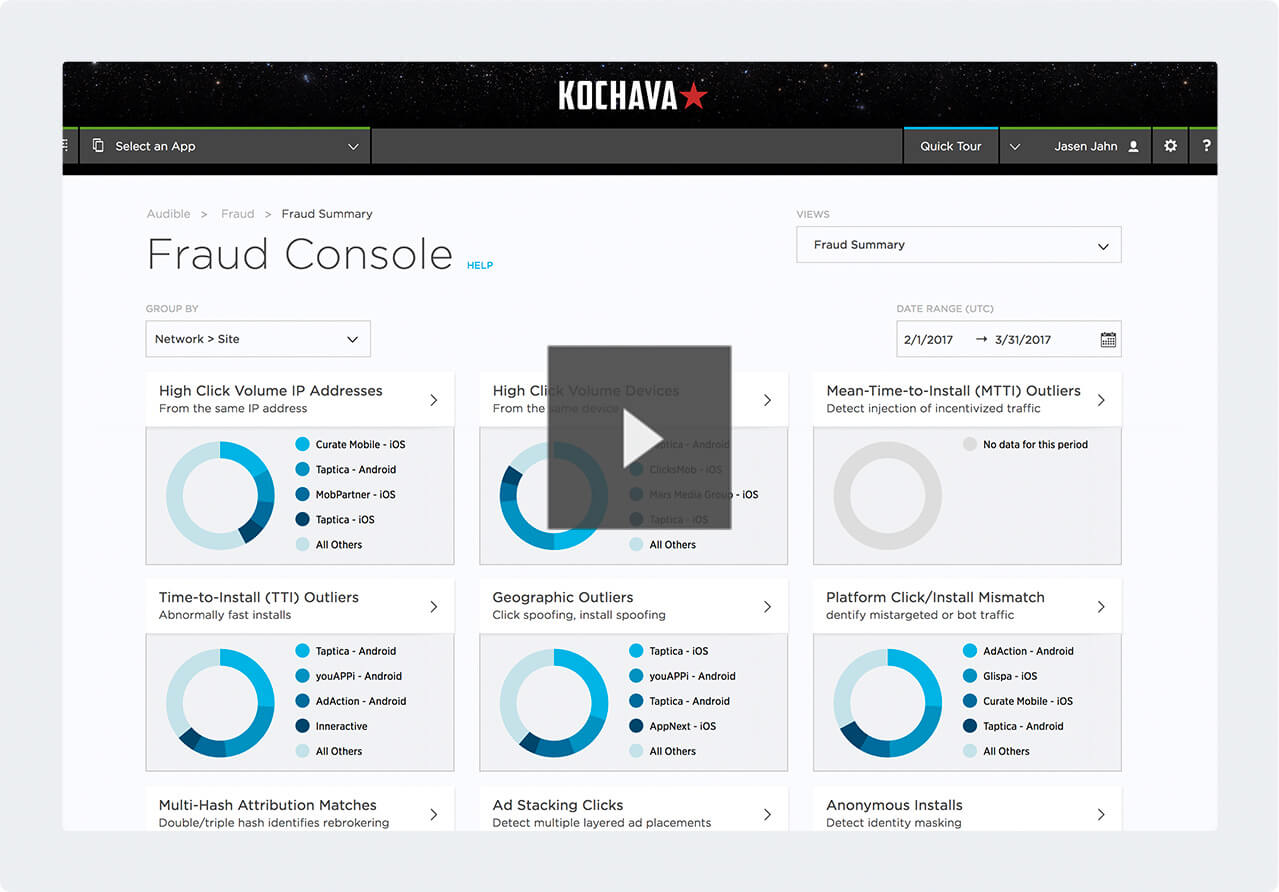
The Kochava Fraud Console for Networks provides industry-leading fraud abatement tools, allowing networks to identify fraud before the advertiser does, and detect fraudulent traffic before paying sub-publishers for it.
The visualizations show both obvious fraud and data anomalies, flagged for review. By using the Fraud Console, networks show their credibility in doing their part to uphold ethical industry standards. Preventing fraud means saving revenue and time spent negotiating amends after the campaign.
Data visualizations of statistical outliers
The console includes 12 reports that leverage statistical methodologies and pattern identification to flag all identifiable fraudulent tactics present in the ecosystem.